Install
Documentation for our customized KeePass Password Safe client - Pleasant Password Server
Hassle free. Worry free. Achieve and move on.
Discover how Pleasant Password Server will enhance KeePass for business
Install Pleasant Password Server with Password Safe the KeePass for Pleasant app.
Sections:
Related Information:
- Upgrade Software
- Uninstall
- Next Steps
- Connecting to Pleasant Password Server
- Server Address
- Remote Access / Accessing Externally
- Client Distribution
- Setting the Website Address
- Settings and Setup
- Other Information
-
Have Questions? Contact Us!
Server Requirements
For server requirements please see the Detailed requirements.
Download
-
Pleasant Password Server includes server-related components:
- Pleasant Password Server
- Server Database
- Web Client - for admin & users
- Service Config Utility - available from the Start menu
-
KeePass Password Safe is downloaded separately - from the web app "Client Download" tab
Install
-
Run the installer
- Ensure the machine has .NET 4.8 installed, and meets the server requirements.
-
Advanced options:
-
To install:
- to script the installer: use MSI Extraction or use these switches
- on Windows Server Core (without Desktop Experience)
-
After installing, you can:
- Host with IIS (switch from the default IISExpress)
- Switch to another database type (e.g. PostgreSQL, MS SQL, Azure DB),
- Move Password Server's database from the default location, or,
- Change the network port it uses (default: 10001).
-
-
Navigate to the startup website, which will launch once installation is complete.
- Click the default server link (https://localhost:10001) to go to your Password Server administrative web site.
- Problems? See the instructions: here
-
Sign in with the default credentials:
User: admin
Password: admin - Change the Administrator password (you'll be prompted to do so). Add a secure and verified email address for admin user(s).
- Note: We strongly recommend keeping & safe-guarding this local Administrator account and password
- Don't get locked out! Setup Password Reset
- Have a backup plan to protect against: forgetting the admin password, admin gets locked out
Congratulations! You have finished installing the software!
- Continue with configuration sections below...
Setup & Configure
Next, setup and configure your Pleasant Password Server.
-
- To assist you in customizing your installation
- More information is provided on this wiki page, in the sections below.
-
- Recommended configurations
-
- We recommend using a valid, third-party signed certificate, which ensures a secure connection between your client device and the server.
-
- An overview
-
- Once you have purchased a license
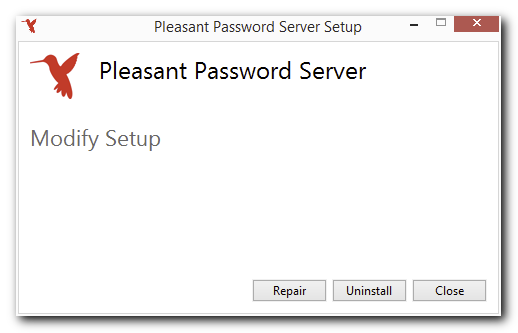
Uninstall
- Open Control Panel > Programs > Programs and Features.
- Select Pleasant Password Server and click Uninstall.
- Click the Uninstall button in the window that appears (shown below).
- (Optional) Remove all traces:
WARNING: After performing the steps below, your data will be unrecoverable.
-
Use the MMC Certificates snap-in to delete PasswordServer_Temporary_Placeholder_Certificate from the Personal store.
-
Delete your database. Database location:
- SQLite
- Other providers: ask your Database Administrator.
-
Delete the following registry keys:
- HKEY_LOCAL_MACHINE\SOFTWARE\Pleasant Solutions\PasswordManager
- HKEY_CURRENT_USER\SOFTWARE\Pleasant Solutions\Pleasant Password Server
-
Connecting to Pleasant Password Server
-
Determine the hostname of the computer running Password Server. On the computer running Password Server, open the Start menu. Right-click on Computer and click Properties. In the Properties window, locate the field Full Computer Name.
-
Using another workstation, point your web browser at the address https://[hostname]:10001, where [hostname] is replaced by the Full Computer Name determined in step 1.
- On this administrative website, all supported clients can be downloaded from Client Downloads.
Note: When connecting to Password Server for the first time in your web browser, you might see a warning about an untrusted site or Certificate. This is due to the default TLS/SSL Certificate that comes with Password Server. This Certificate is Self-Signed (as opposed to being signed by a Trusted Certificate Authority) and also does not match the Domain Name that is being used to access your admin website. For internal company use, this Certificate is safe and this warning can be safely ignored. You can find instructions on configuring a custom Certificate here.
Server Address
By default, Pleasant Password Server has a URL in the form of https://hostname:port to connect with your server instance.
If no port number is specified in the URL, port 10001 is used by default. If you change the port number of your server, you must specify that in your URL. (see Port Configuration)
As with any web service, the server will respond to any traffic on its assigned port.
Client Login
Clients will accept the server address if you forgot to specify https:// or a port number.
So, if on an intranet, these server addresses:
- passwords.yourdomain.com
- passwords.yourdomain.com:10001
- http://passwords.yourdomain.com
- https://passwords.yourdomain.com:10001
will *ALL* be redirected to:
-
https://passwords.yourdomain.com:10001
Client Distribution
Customers will have varying methods and policies for deploying / distributing & installing the KeePass for Pleasant client on user machines.
-
Using a deployment platform such as:
- MECM (formerly: SCCM & Intune)
- GPO (AD Group Policy)
- PDQ Deploy
- or another tool
-
User downloads from "Client Download" tab in web app: visible to all with Users role ("View Client Download")
- Setup an internal fileshare with the client download files
An MSI package may be used in an enterprise situation. Below are some additional links that may be helpful.
Links:
- MSI Extraction
- Installing Your Certificate on Other Machines
- KeePass Setup Switches
- Default the KeePass Server URL
Configure Default Server
For the KeePass for Pleasant client, it is possible to set the default Server URL and/or Username. These values can be scripted at the time of each User's initialization setup, to add/modify the default values into the user's AppData Roaming profile.
This file gets created for each user automatically after their first login, unless it already exists there.
Full path:
- C:\Users\USERNAME\AppData\Roaming\PleasantKeePass\PasswordServerClientConfiguration.xml
Shortened path:
- %AppData%\PleasantKeePass\PasswordServerClientConfiguration.xml
Keys to modify/add:
- <PasswordServer>https://passwords.yourdomain.com:10001</PasswordServer>
<UserName>username</UserName>
Accessing from a Remote Location
By default, Pleasant Password Server runs on port 10001. If you want to access your passwords from a remote location, you may need to forward this port in your firewall settings. (see Port Configuration)
Note: Pleasant Password Server will automatically try to add firewall rules for Windows Firewall. These rules will be removed when the service is stopped or uninstalled.
Configuring External Access
For external access, configuration is as easy as installing the server for local use, with the exception that you must have your network infrastructure configured properly.
Benefits:
- Traffic from the internet will need to be routed to your password server hosted internally.
- Be aware of security implications of opening ports in your firewall to the internet.
Methods:
-
Virtual Private Network (VPN)
- Allow access using a virtual private network app - Configure network router, firewall, and possibly other network resources
-
Web Application Proxy
- Publish internal applications externally, ensuring that only authenticated connections hit your network
- Provides secure access to internal applications from external networks
- Use with the Pre-Authentication setting option
-
Examples:
-
Microsoft Entra Application Proxy - details: Microsoft Entra / Azure AD Integration
-
- Publish internal applications externally, ensuring that only authenticated connections hit your network
-
Reverse Proxy
-
Provides a security layer that manages and optimizes traffic with features like load balancing and scaling
-
- Web Application Firewall (WAF) / Application Gateway
-
Secure and optimize traffic
-
-
Port Forwarding
- Redirect internet traffic to Password Server. Read more about port configuration.
Additional Safeguards:
Depending on the method you choose above, you may consider these configuration options.
-
Require Two-Factor Authentication
-
IP Filtering:
- Configure the Firewall to selectively open access to specific IP address ranges
- Provide external users with appropriate access
- IP filtering options are available when hosting with IIS and are configurable in User Policies from Password Server.
-
(Advanced) Use Client Certificate Authentication, possible with IIS Hosting
In the rare circumstance of completely separate environments with no connectivity, multiple instances can be configured
Setting the Website Address
The port number can be changed in the Service Config Utility (see Port Configuration), and it is possible to switch your servername by migrating to another machine.
It is also possible to change the URL using various other methods (see Redirect to HTTPS):
- Use an internal DNS redirection (see Using a Different Server Name)
- Host with IIS and set the site bindings
- Redirecting incoming requests to another URL / another port
- Re-write the URL (technical)
Then, if any URL redirection changes have been made in your environment (unknown to Password Server), you can then change the Display URL to align with those changes, from the General Settings in web administration.
Using a Different Server Name
Using an internal DNS, you can add an alias (CNAME) with an entry pointing to the server. Then all clients on your intranet or VPN can easily access the server via any name you choose.
In a Windows environment, you can also access it using the computer name (i.e Server123).
- This function relies on NetBIOS resolution and has to be the name of the server only.
- In a smaller environment, it is possible to also just modify the hosts file for all workstations accessing the server, but this is not a scalable long-term solution as it is difficult to update.
Settings and Setup
Roles
Roles allow multiple users to be given the same entry/folder access. They are also the only way to assign server-wide permissions ("permissions") like the ability to view logs or edit users. Roles can inherit both permissions and access from other roles; if the roles Developer and IT are made sub-roles of DevOps, DevOps inherits the permissions and access of Developer and IT combined (DevOps-specific permissions and access can be added separately).
Important: the Administer Users permission should be treated as the keys to the kingdom - all permissions and full access to all entries and folders - because a user with only this permission (via his role) can simply make his role the parent of any other role to gain the latter's permissions and access.
Access Levels
An Access Level is simply a name for a group of permissions assigned as a unit. Password Server ships with several built-in Access Levels: Full, Full + Grant, and Full + Grant + Block (see here for an explanation of Block). Enterprise and higher editions add a fourth built-in level (Read-only) and allow the creation of entirely new Access Levels (eg, perhaps you'd like some admins to have broad access-granting abilities but no password access themselves? Create an Access Level with only G permissions!).
Access Levels are a key feature in Pleasant Password Server (PPASS) which let you control access (both per-user and per-role) to actions such as Adding, Deleting, and Viewing Entries and Folders. Each of these actions (see here for an full listing) has two associated permissions: A ("Action") permits the action itself, while G ("Grant") permits the holder to assign the corresponding A permission to other users (the special, G-only "Permissions" action alters each of the other G permissions so that it permits the holder to assign itself in addition to the corresponding A). A good understanding of G permissions, in particular, is necessary for such common tasks as the creation of sub-admins with responsibility over some portion of the folder tree.
Note: An access level that is in use cannot be deleted. Click the "In Use" button attached to any such Access Level to see a list of use sites.
To add or remove access on a particular folder (and everything nested within it - access is inherited!) or credential, click the (Folder) Actions button and select Security (the default Admin user has Full + Grant + Block (every available permission) access on the root of the folder tree, and thus on all folders and credentials except those on which Access Inheritance has been blocked).
User Settings
Use the Settings page to control Private Folder defaults, the visibility of menu entries, custom branding, and the setup of email sending by Password Server.
Other Information
Database
Pleasant Password Server automatically uses a SQLite database to store your password and user configuration data. If you would prefer to use MS-SQL or PostgreSQL, you use the Service Configuration utility installed alongside Password Server. This page provides more detail regarding use of other supported databases.
Structuring the Password Server and KeePass Client
For information on how to structure your Pleasant Password Server and/or your KeePass Client, click here.
Trouble?
If you having issues getting set up, you may want to view our video Setting Up Pleasant Password Server (legacy link).
If you have any further problems or questions:
- FAQ / Common issues for answers to your questions
- Troubleshooting for tools/contacting us to help diagnose problems
The Pleasant Solutions support team would be happy to help you.
