Setup Folder Permissions
See why customers enjoy using Pleasant Password Server with a KeePass client
Included is an explanation of the permission structure, and a few sample folder structures are provided. These will give you ideas towards setting up your organization's permissions.
Other Related Topics:
Setup Password Folders
Department Team Access
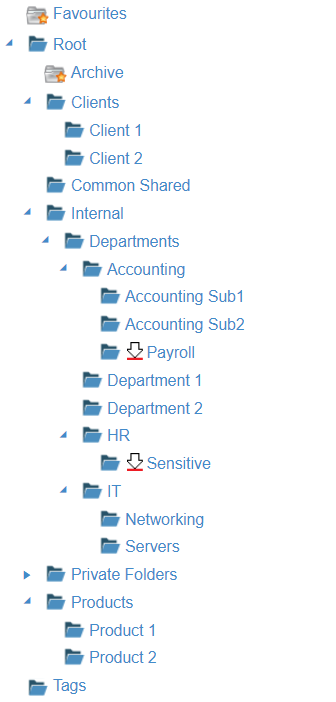
Department Teams can be separated into their own folders, and assigned their own levels of access. Below is a great example of what an organization folder may look like.
To get started, first add branches under the Root folder, for example:
- Clients
- Client 1
- Client 2
- Common Shared
- list of things all employees access
- Internal
- Departments
- Department 1
- Department 2
- Departments
- etc.
Example Folder Structure
Example of Granting User Access
Here is an example of assigning access to user roles on these folders. This explains what access the users/roles will have when granted.
Granting Access to a User or Role:
-
Add access for role A: directly on Root folder
-
A will inherit access to everything, all subfolders, and entries including: Accounting, Department folders, HR, IT, etc.
-
- Add access for role B: with access on IT
-
B will also have access to IT, Networking, and Servers
-
- Add access for role C: with access to IT and HR
-
C will NOT have access to Accounting, Department 1, or Department 2
-
- Add access for role D: with access on Accounting Sub1
-
D will only have access to Accounting Sub1
-
Folder Permission Structure
The permission structure is hierarchical.
User access is usually assigned on a folder (e.g. Root):
-
Folder Access will include access everything underneath it: all Folders / Subfolders / Entries (see example above).
- New subfolders / entries will also be automatically accessible.
- The permissions automatically spread throughout the whole subtree underneath
-
Access can be Blocked: the access continues until a Sub-Folder or sub-Entry is Blocked.
User Role:
- By default users are given the User role. Providing access to this role is giving access to everyone.
Administration Role:
- By default the admin user is assigned the Administration Role on the Root folder. It will have access to everything below it, unless the permission inheritance is manually Blocked.
-
For examples of using restricted administrative users, see: Limited Admin Access
